Encrypting ransomware (also called cryptolockers) has been in the news a lot recently. For those of you who haven’t heard of it, cryptolockers are a type of Trojan malware specifically targeted at computers running the Windows OS (operating system). These Trojans can encrypt a certain amount of computer files (mostly based on the file type). They then request a ransom (bitcoins) in exchange for the deciphering key. The biggest problem with these types of malware is that even after you successfully remove the malware, the files will remain encrypted. If you don’t have a cryptolockers backup strategy, you will lose all your files. Worse, there are reports of people paying the ransom to get their files back, but still not receiving the deciphering key.
And cloudHQ is built with protection against cryptolockers in mind. When you create a cloudHQ backup sync pair, you also get a cloudHQ real-time data protection. In other words, cloudHQ ensures that every single iteration of your data is recorded, with past versions securely stored in the cloudHQ_archive folder. Thus, if your files are encrypted by cryptolocker, you do not need to worry because the prior version of the files are backed up and stored in cloudHQ_archive folder.
This means that cloudHQ is capturing every single version of your data, and previous versions of your data are saved in the cloudHQ_archive folder. So, if some files get encrypted via cryptolocker, the previous version of a file will be automatically saved in the cloudHQ_archive folder.
So for example, if ransomware happens on 1st of Jun 2020 at 18:00, then an unencrypted version of all your storage and files will be under: Amazon S3/backup_bucket/cloudHQ_archive/2020/Jun 2020/01 Jun 2020 (wed)/2016-06-01T18:00:00
This allows the user or administrator to restore data to a point in time before crypolockers started encrypting the files. You can think about cloudHQ sync as a very powerful version of Apple Time Machine for your data in the cloud.
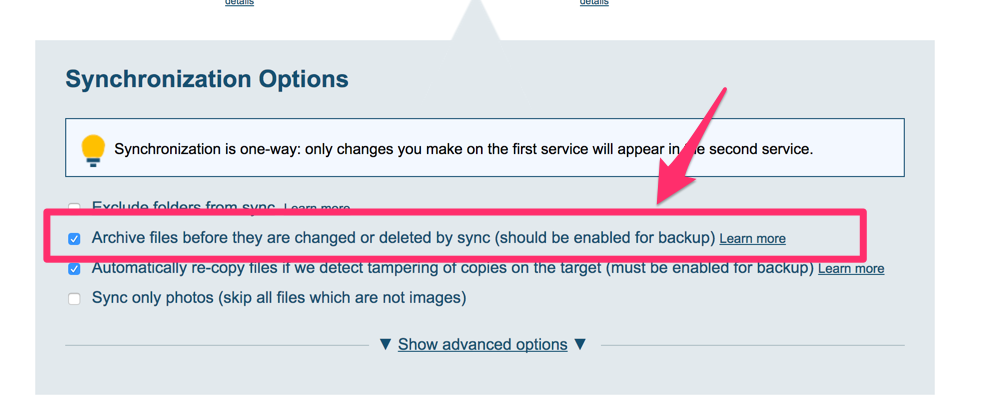
The key here is that you enable the option “archive files before they are deleted or modified” for your backup sync pairs.